DOES YOUR ORGANIZATION HAVE A RISK ACTION PLAN?
 (Can you afford not to?)
(Can you afford not to?)
Targeted attacks, human and system errors, structural failures, operational disruptions due to natural disasters… These events are in the news every day.They compromise the confidentiality, integrity, and availability of information systems, and have tremendous adverse affects on organizational operations, assets, and people. These affects can even endanger other organizations and national interests. You know your organization needs to defend against these threats, but the realities of budgeting often get in the way.
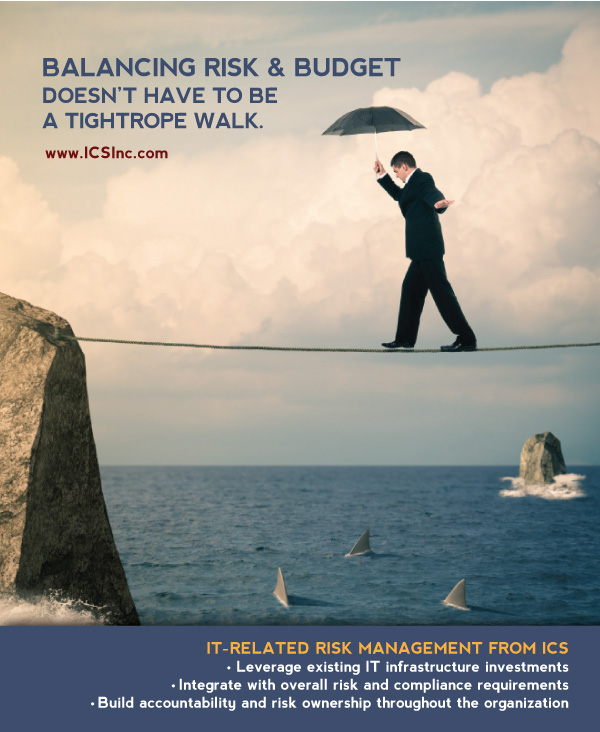
Risk is inherent in all organizations. It cannot be totally avoided. Can risk and budget be assessed simultaneously to determine how much risk is tolerable? The answer is YES and ICS can show you how.
Managing risk appropriately provides tremendous business value, improving all facets of information security. Learn more about how your organization can develop a Risk Action Plan in this free resource from ICS.
Make the most of your IT security investment.
So, what is an acceptable level of risk, and how is that level determined? The Risk Management process will help answer these questions by taking a strategic and proactive approach, beginning with an evaluation to determine risk tolerance, and followed by a thorough documentation of risk policies and regularly scheduled risk assessments to evaluate risk factors and maintain risk standards. Efficient IT risk management is a smart approach that can have a positive impact on your security investment.